Risks in Data Collection

Companies collect personal data for a number of different reasons, mainly targeting ads to increase sales. However, the risks of collecting personal data is that if the company with the data is breached, said data can be used for malicious purposes. For example, if someone obtained information, they could use it to commit fraud and identity theft, such as moving money from bank accounts. This personal data could include Social Security numbers, Credit card and Bank Numbers, as well as others.
However, there are measures that can be put in place to safeguard this information. The Federal Trade Commission (FTC) recommends that companies follow four simple steps: Take Stock, Scale Down, Lock It, and Pinch It. To put it simply, The guidelines suggest that these companies understand the data they already have in various locations, such as files, computers, hard drives, and other means of storage. Then they need to remove any information that is not crucial to their business, and “Pinch it” or effectively remove it, by means of shredding and entirely wiping electronic data. Finally, and most importantly, companies should “Lock It,” or secure said data by means of physical protection, such as vaults or safes, electronic protection, by means of firewall, and future protection, by training employees to be prepared to deal with such data breaches. Here is the FTC's actual website that goes more in depth on the subject.
An example of a major data breach was in 2013, when Apple’s developer portal was compromised, allowing hackers to obtain roughly 275,000 user’s data. This data consisted of the user’s name, email address, as well as home address. After this devastating data breach, Apple began to reinforce their security systems, by adding the Secure Enclave to modern Apple products starting in 2013, which is a hardware-based security system. On top of new hardware security, Apple introduced two new software based security systems, the Two-Factor Authentication in 2015, and the Advanced data protection system for iCloud in 2023. For more on this, check out Forbes' Article as well as Twingate's article.

Misuse of Personal Info

There are several examples of people misusing technological resources, often time with malicious intent. One of the most well known examples are malware and computer viruses. Instead of using files and sharing to its intended use of sharing information, hackers began to abuse this system by sending files filled with computer viruses and gaining access to crucial computer systems. Another example of using computer messaging is harassment and violation of another’s privacy, by means of gaining personal information. This list by SUSLA is an example of the proper use of technology.
However, similar to other strategies of protecting one’s self online, users can follow a few steps to ensure their safety. The first measure is to get the most recent software patches, which typically contain security patches. Then, the user can monitor who they give access to their system, usually by changing passwords and only entrusting it to extremely trustworthy people. Finally, the user can gain an understanding of identifying how malware enters their system. Here is the CISA's Website on proper user Cybersecurity.
An example of a real misuse of computer resources was in early August, 2019 through an employee at the cybersecurity firm Trend Micro. This employee used their position in the company to gain access to roughly 68,000 user’s personal information, which they sold to a malicious third party. These 68,000 people’s phone numbers, as well as other information, was used to conduct thousands of scam calls. It was only in mid-August that the company became aware of the breach in data, and put an end to the scam calls. After this disaster, Trend Micro was essentially forced to upgrade their security measures on both customer and company sides. Visit Threat Post's article for a more in-depth look at the Trend-Micro incident.

Unauthorized Info Access
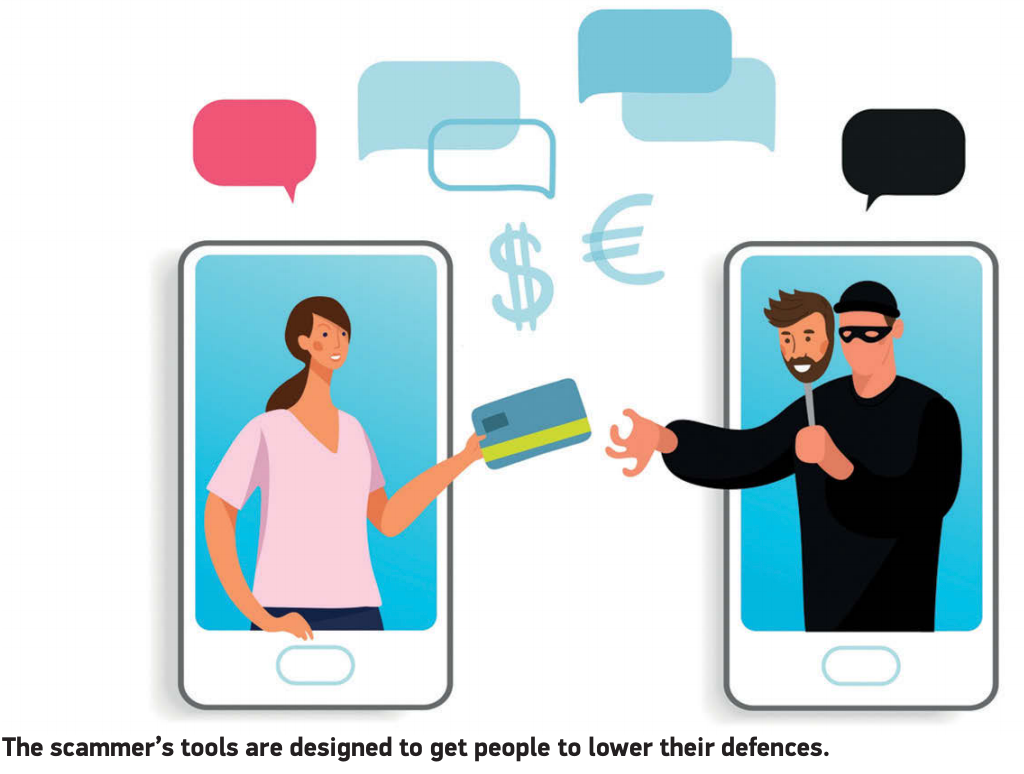
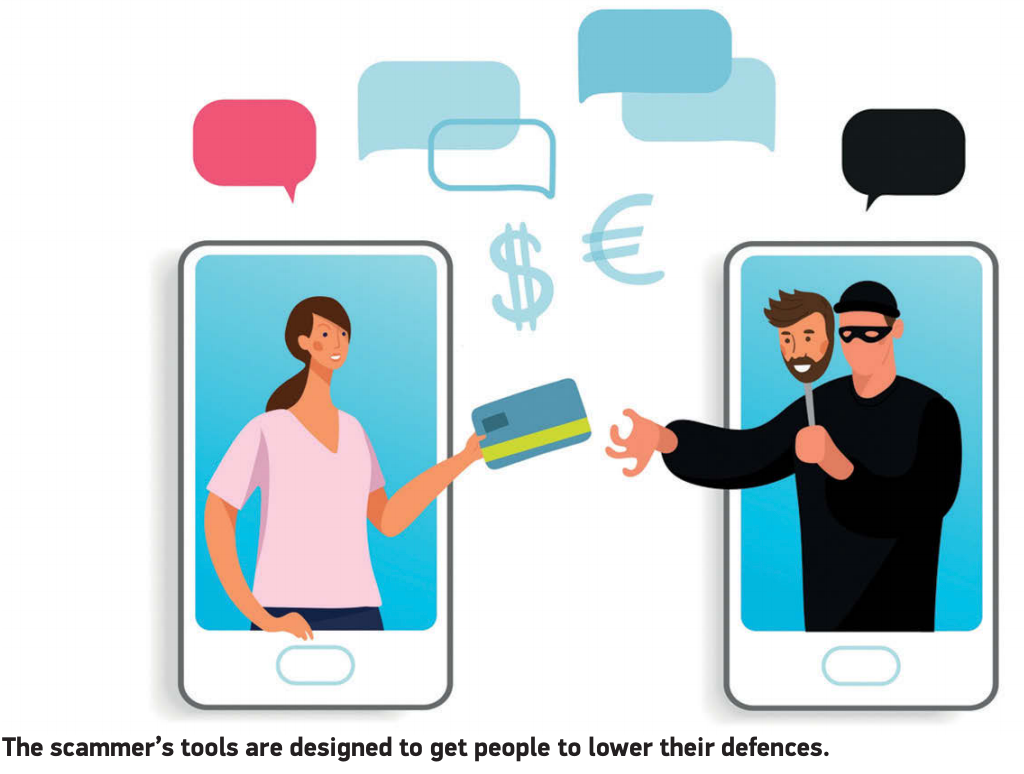
Information is one of the most important aspects to online use, which allows users to gain access to accounts, make purchases, and other uses. However, this information can be accessed by people outside of the user’s knowledge. There are several ways to gain access to information, mainly through two techniques, Social Manipulation and Computer Software Manipulation. Social Manipulation involves when the hacker uses human error such as not verifying emails and phone numbers to coax logging information. The Technological side of the issue is a whole other topic, in which the hacker utilizes programs designed to gain information on the user’s computers, such as passwords from viruses inside the computer, typically shared from other computers. For more on this, check out Kaspersky's Website
Not all hope is lost, however, and there are ways the user can ensure the safety of their information. On top of helping large corporations, the FTC also guides people through ways they can ensure their own personal information. The FTC recommends several safeguards, mainly through mindfulness of networks and downloads, keeping software in track, and understanding well-developed passwords. In their article, the FTC recommends that passwords be specific to the person as possible, and that Two-Factor Authentication also be used, utilizing similar specifications to the person like passwords. However, users can go many steps farther, and be sure that their operating systems are running on the most modern, and thus most safe, system, as well as securing their personal network. Check out the FTC's article for more protection tips.
An example of a larger gaining of Unauthorized Access to information is the Equifax breach in 2017. This data breach was a combination of two main factors, both outdated software on Equifax’s side, as well as many poor password combinations on the User’s side. Over 147 Million people were affected by this breach which led to almost all of those having their Social Security Numbers being breached. This caused the company hundreds of millions in expenses. After this, Equifax pushed several new security measures, and encouraged users to utilize stronger passwords. See Huntress' article on the Equifax-Netflix Data Breach.

Usage of Computing Inovations

There can be several outcomes to a Computing Innovation, which could be good or bad. An example of a two-sided computing innovation would be the messaging system. An example of a good outcome would be that messaging systems allow for quick information to be exchanged and information of medical help to easily be sent to the patient. However, those same messaging systems can cause harm as well, including talking to strangers, a decrease in physical communication, and spread of false information. This shows how messaging systems can have both negative and positive factors connected to them.
An example of unintended use of technology would be the online video system, mainly Youtube. The Original Creators, Chad Hurley, Steve Chen, and Jawed Karim, initially intended Youtube to be a fun video sharing app. However, after twenty-one years of operating, Youtube has turned into a recreational way of entertainment, with several, complex forms of watching videos. Another form of this would be GPS, which was intended to help locate people when in need. Now, GPS can maliciously be used to locate people and use said information as leverage to gain things. Albert.io's Website several examples of Computing Innovations, but most importantly, about Social Media.
Another example would be the increase of AI use in modern history. Originally, AI was created to solve extremely complex mathematical problems, but after an innovation in the 2020s, AI became smarter than ever. While AI does have several advantages, such as helping people learn, solve problems, and other things, it also has negatives. A few examples of these negative effects are that people use AI to do their work instead of teaching them, trusting AI completely instead of researching themselves, and other issues. The complete stray from its original purpose has caused many CEO’s of companies to withdraw the use of AI from everyday life, such as Dario Amodei, the president of Anthropic, who did not allow the United States government to unrestricted use of its AI program. Check out Tableau's site for more on AI and its benifits and Concequences.
Elements
Text
This is bold and this is strong. This is italic and this is emphasized.
This is superscript text and this is subscript text.
This is underlined and this is code: for (;;) { ... }. Finally, this is a link.
Heading Level 2
Heading Level 3
Heading Level 4
Heading Level 5
Heading Level 6
Blockquote
Fringilla nisl. Donec accumsan interdum nisi, quis tincidunt felis sagittis eget tempus euismod. Vestibulum ante ipsum primis in faucibus vestibulum. Blandit adipiscing eu felis iaculis volutpat ac adipiscing accumsan faucibus. Vestibulum ante ipsum primis in faucibus lorem ipsum dolor sit amet nullam adipiscing eu felis.
Preformatted
i = 0;
while (!deck.isInOrder()) {
print 'Iteration ' + i;
deck.shuffle();
i++;
}
print 'It took ' + i + ' iterations to sort the deck.';
Lists
Unordered
- Dolor pulvinar etiam.
- Sagittis adipiscing.
- Felis enim feugiat.
Alternate
- Dolor pulvinar etiam.
- Sagittis adipiscing.
- Felis enim feugiat.
Ordered
- Dolor pulvinar etiam.
- Etiam vel felis viverra.
- Felis enim feugiat.
- Dolor pulvinar etiam.
- Etiam vel felis lorem.
- Felis enim et feugiat.
Icons
Actions
Table
Default
| Name |
Description |
Price |
| Item One |
Ante turpis integer aliquet porttitor. |
29.99 |
| Item Two |
Vis ac commodo adipiscing arcu aliquet. |
19.99 |
| Item Three |
Morbi faucibus arcu accumsan lorem. |
29.99 |
| Item Four |
Vitae integer tempus condimentum. |
19.99 |
| Item Five |
Ante turpis integer aliquet porttitor. |
29.99 |
|
100.00 |
Alternate
| Name |
Description |
Price |
| Item One |
Ante turpis integer aliquet porttitor. |
29.99 |
| Item Two |
Vis ac commodo adipiscing arcu aliquet. |
19.99 |
| Item Three |
Morbi faucibus arcu accumsan lorem. |
29.99 |
| Item Four |
Vitae integer tempus condimentum. |
19.99 |
| Item Five |
Ante turpis integer aliquet porttitor. |
29.99 |
|
100.00 |